Corporate Presentation
Download our Teknei presentation to learn in detail everything we can do for you.
Self-Managed Verifiable Identity
Teknei is a pioneer in the development of Decentralized Digital Identity solutions (known as DID or Self-Sovereign Identity, SSI).
Thanks to Blockchain technology, we have developed projects that create a new realm of trust for interacting reliably and securely through electronic means with verifiable digital credentials.
Issues and verifies verifiable credentials, the digital identity model that best solves the security, privacy, and efficiency problems of digital processes.
The issuer issues digitally signed certified credentials.
The holder manages credentials and presents them to verifying entities.
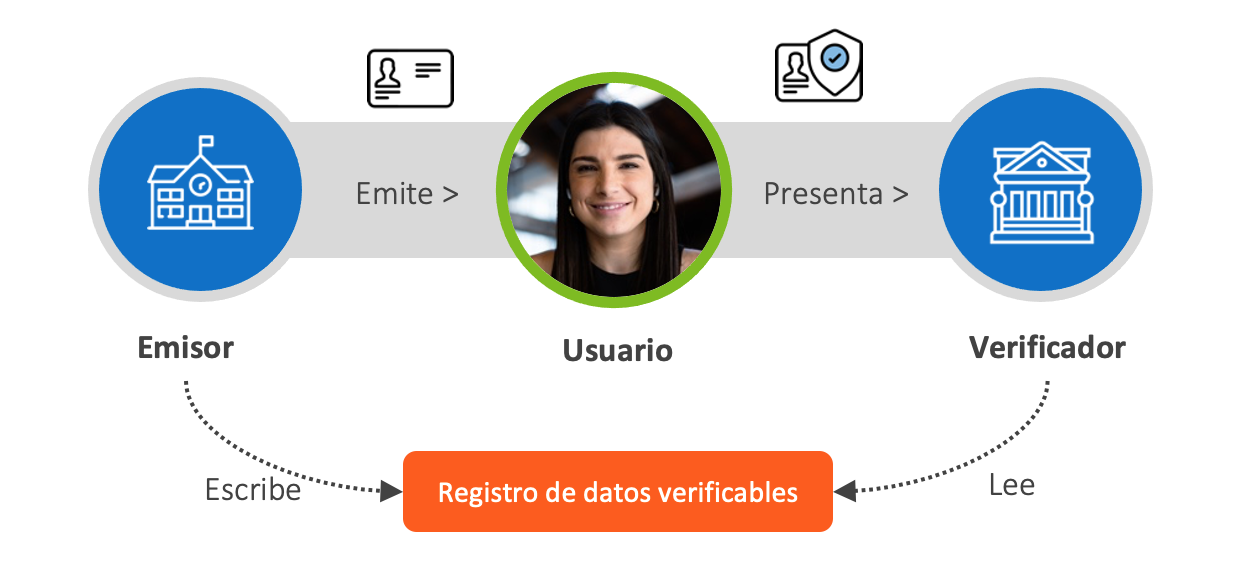
The verifier requests proof and verifies that the issuer's credentials meet the requirements and are correctly certified by a valid issuer.
Based on open standards, verified identity automates the verification of identity credentials and enables privacy-protected interactions between organizations and individuals.
The key aspects of Decentralized Digital Identity are:
- Sovereign Information: Certified information of each person is managed and controlled by the user, who has complete control over their data, ensuring their privacy.
- Digital Information: Data exists in a digital environment, essential for exchanging information quickly, securely, and reliably with other individuals or institutions.
- Interoperable Information: It can connect to different verifiers each time credentials need to be presented.
- Decentralized Information: Managing personal data on a Blockchain network allows storing and individually protecting all individual information and ensuring its integrity.
- Secure and Reliable Information: unquestionable information in an incorruptible environment.
- Certified Information: The information has a digitally signed certification from the issuer.
Digital
Secure and reliable
Certified
Sovereign
Decentralized
Interoperable
Business Partners